6.7 KiB
F2B Control Center — User Guide
A plain-English walkthrough of the dashboard. No technical background required.
What It Does For You
F2B Control Center watches the traffic hitting your self-hosted services and automatically bans IP addresses that are behaving badly — bots scanning for security holes, scrapers hammering your error pages, tools probing for WordPress vulnerabilities on a site that isn't even WordPress.
When something gets banned, it's blocked at the server level. The banned IP can't reach any of your services, not just the one it was probing.
The dashboard gives you a live view of what's happening, and lets you take action on anything you see.
Opening the Dashboard
Navigate to http://YOUR_SERVER_IP:4000 in your browser.
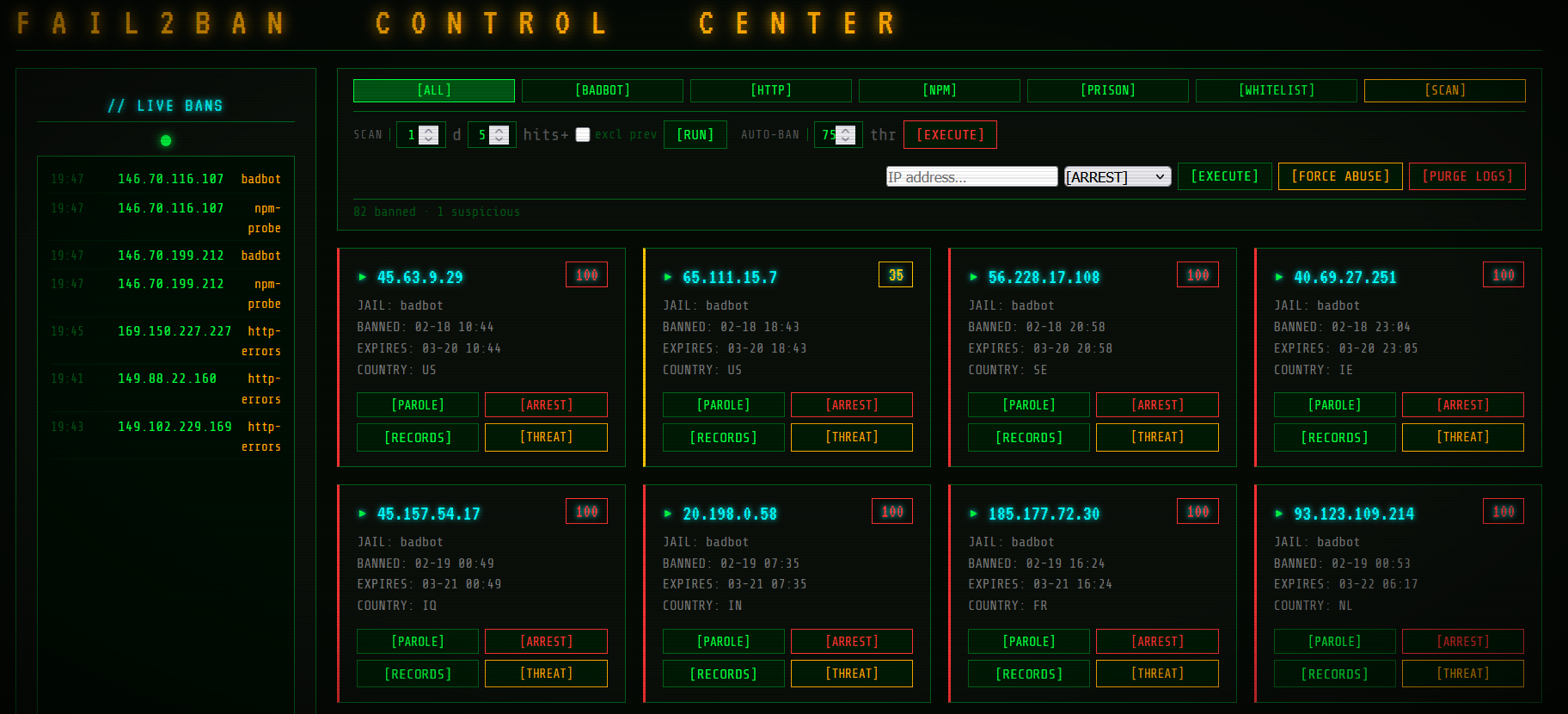
The Ban Grid
The main view is a grid of cards — one card per banned IP address.
Each card shows:
- The IP address that was banned
- Why it was banned — shown as a badge (see Jails section below)
- When the ban expires — or "permanent" for manual bans
- Threat score — a 0–100 number from AbuseIPDB showing how widely this IP is known to be malicious (only shown if AbuseIPDB is configured)
Jails — Why Was This IP Banned?
Every ban comes from a "jail" — a rule set that detected bad behaviour:
| Badge | What it caught |
|---|---|
[BADBOT] |
The IP's browser/tool identified itself as a known scanner or hacking tool (masscan, sqlmap, Nikto, etc.) |
[NPM-PROBE] |
The IP tried to access classic exploit targets — WordPress logins, .env files, PHP shells, admin panels — paths that have no business being requested on your server |
[HTTP-ERRORS] |
The IP generated a flood of 4xx or 5xx error responses in a short time window — typical scanning or brute-force behaviour |
[PRISON] |
You manually banned this IP |
[WHITELIST] |
This IP is fully trusted and will never be banned or flagged |
[EXEMPT] |
You've reviewed this IP and dismissed it — it won't appear in scan results, but the system is still watching it |
Filter Tabs
The row of buttons across the top filters the grid:
- Click
[ALL]to see every banned IP at once - Click any jail name to show only that group (e.g.
[BADBOT]to see only bot traffic) - Click
[SCAN]to run the log scanner (see Scan section below)
Actions — What You Can Do With a Banned IP
Each card has buttons for acting on that IP:
| Button | What it does |
|---|---|
[RECORDS] |
Opens the access log for that IP — every request it ever made to your server |
[PAROLE] |
Removes all bans for this IP and lets it through again |
[ARREST] |
Manually bans this IP permanently (useful from scan results) |
[THREAT] |
Looks up this IP on AbuseIPDB — shows its global reputation and recent abuse reports |
[WHITELIST] |
Marks this IP as fully trusted — fail2ban will never ban it again |
[EXEMPT] |
Dismisses this IP from scan results without trusting it — it stays monitored |
[REMOVE] |
Removes an IP from the whitelist or exempt list |
The Action Bar
The bar just below the filter tabs lets you act on any IP by address — even ones that aren't currently banned:
- Type or paste an IP address
- Choose an action from the dropdown
- Press
[GO]
Actions available here:
[ARREST]— ban immediately, permanently[PAROLE]— remove all bans[WHITELIST]— trust this IP permanently[SEARCH]— highlight cards matching this IP in the current grid view
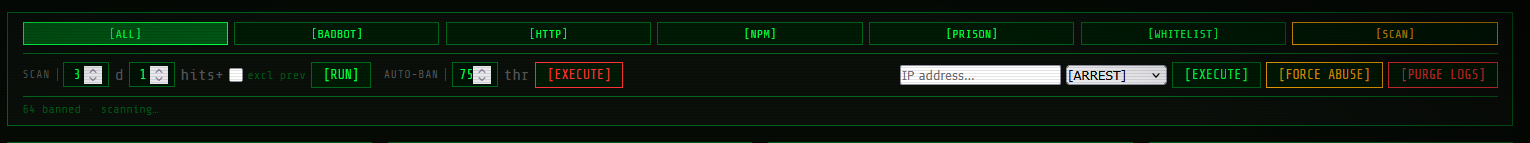
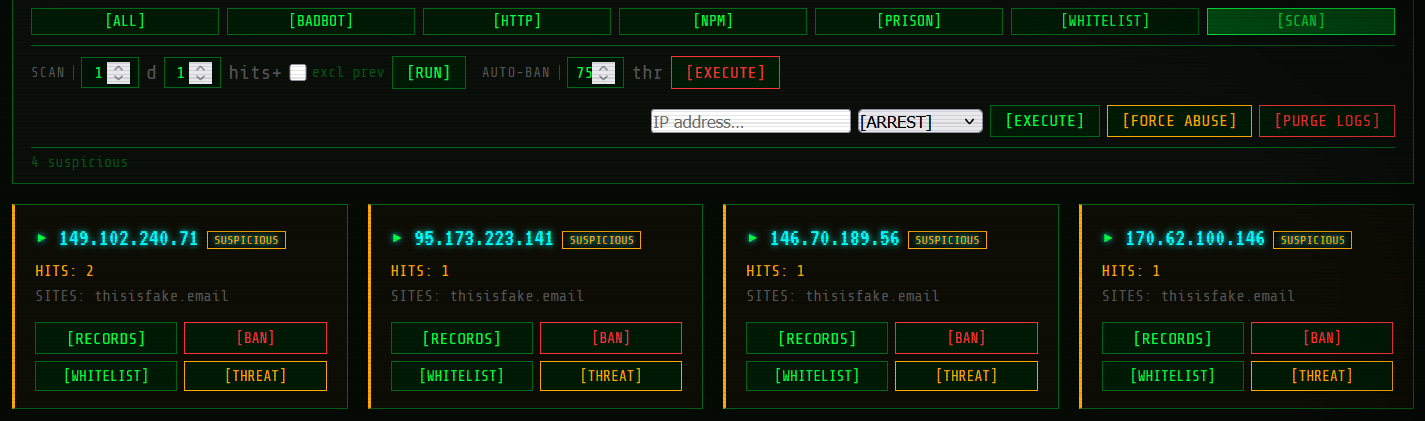
Scan
The Scan reads your NPM access logs and surfaces IP addresses that are behaving suspiciously but haven't been banned yet. Click [SCAN] in the filter tabs to run it.
It looks for IPs that are:
- Generating lots of errors
- Hitting known exploit paths
- Using scanner user-agents
From each scan result card you can:
[BAN]— ban it right now[EXEMPT]— mark as reviewed; hide from future scans (monitoring continues)[THREAT]— check its reputation on AbuseIPDB[RECORDS]— see everything it requested
The scan is the best place to start when you first set things up. Run it after a day or two of traffic to get a sense of what's been probing your services.
Whitelist vs. Exempt
These are two different levels of "leave this IP alone":
Whitelist is for IPs you fully trust — your own devices, uptime monitors, your office network. Fail2ban will never ban them. They won't appear in scans or the ban grid.
Exempt is for IPs you've looked at and decided aren't worth worrying about right now. They disappear from scan results so they don't keep coming up, but fail2ban is still watching them. If they start misbehaving later they'll get banned normally.
When in doubt about an IP you've reviewed: use Exempt. Reserve Whitelist for things you're certain about.
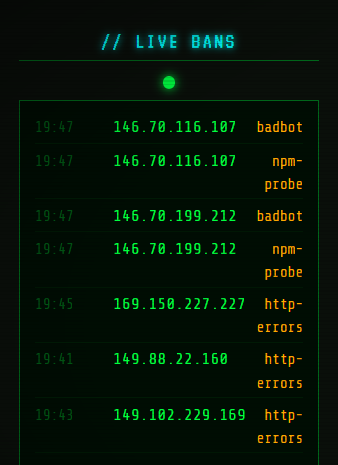
Live Log
The live log shows fail2ban's activity as it happens — every detection, ban, and unban in real time. Useful for confirming that a ban landed, watching a scan in progress, or just seeing what's hitting your server right now.
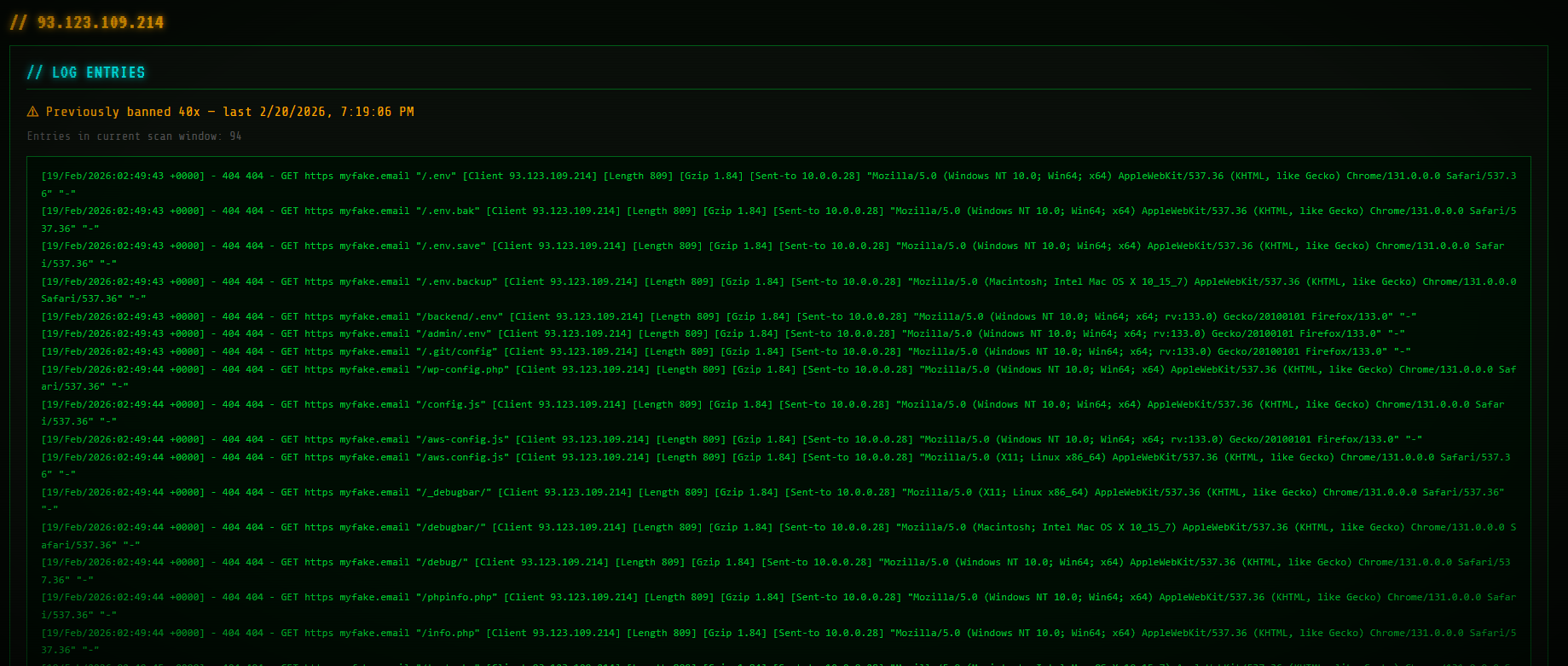
Access Log Viewer (Records)
Click [RECORDS] on any ban card or scan result to open a filtered view of the NPM access log for that specific IP. You'll see every request it made — what paths it hit, what status codes it got back, and when.
This is useful for understanding why something was banned, or deciding whether to parole an IP that might have been caught by a threshold incorrectly.
Tips
- First time setup: Run a Scan after your server has been running for a day or two. It'll show you what's already been poking around.
- False positives: If a legitimate service keeps getting banned, check its access log with
[RECORDS]to understand why. Then either[WHITELIST]it (if you fully trust it) or raise themaxretrythreshold in the jail config. - Recidive jail: Disabled by default. Enable it after your other jails have been running for a while — it gives repeat offenders a 7-day ban automatically.
- Manual bans are permanent: Bans placed via
[ARREST]or the action bar don't expire. Use[PAROLE]to lift them. - Cloudflare users: With
CF_EMAILandCF_APIKEYset, every iptables ban also creates a Cloudflare firewall rule — the IP gets blocked at the edge, before it reaches your server at all.